
Do I Need to Worry About the New Russian Hack, VPNFilter? Maybe.
Posted 01 Jun at 4:42 pm in Security
Do I need to worry about VPNFilter?
 We’ve had a few conversations with customers this week about the new VPNFilter virus from Russia, what it is and if they need to worry. The FBI has reiterated their guidance that users should reboot their routers. If you’re a customer of ours, have no fear, this attack has been limited to what we’d call “residential grade” routers, routers really designed for home use and security. We would never put one of these in your office. Often these devices are the first things we get rid of for our smaller business customers.
We’ve had a few conversations with customers this week about the new VPNFilter virus from Russia, what it is and if they need to worry. The FBI has reiterated their guidance that users should reboot their routers. If you’re a customer of ours, have no fear, this attack has been limited to what we’d call “residential grade” routers, routers really designed for home use and security. We would never put one of these in your office. Often these devices are the first things we get rid of for our smaller business customers.
For home users though, look out. Even if your router isn’t on the list below, we think rebooting your router is a good idea (turn it off and on again). Your internet will down for a minute or two, and you may minimize the risk if routers they didn’t expect are infected. Below you find the complete list of routers that have been affected by the VPNFilter hack and a link to where you can download a “clean” version of the firmware. If you have one of these routers DO THIS IMMEDIATELY or call us, we can help.
- Linksys E1200
- Linksys E2500
- Linksys WRVS4400N
- Mikrotik RouterOS for Cloud Core Routers: Versions 1016, 1036, and 1072
- Netgear DGN2200
- Netgear R6400
- Netgear R7000
- Netgear R8000
- Netgear WNR1000
- Netgear WNR2000
- QNAP TS251
- QNAP TS439 Pro
- Other QNAP NAS devices running QTS software
- TP-Link R600VPN
For those of you with the following models of routers, you DEFINITELY need to reboot and set your routers back to factory default. It could be a bit tricky so if you’re stuck, give us a call and one of our amazing folks can help. We think a lot more routers will be discovered than this, but as of now, this is what have been discovered in the wild. There are currently 500K devices affected right now says the FBI.
Interested in how this works? Read On…
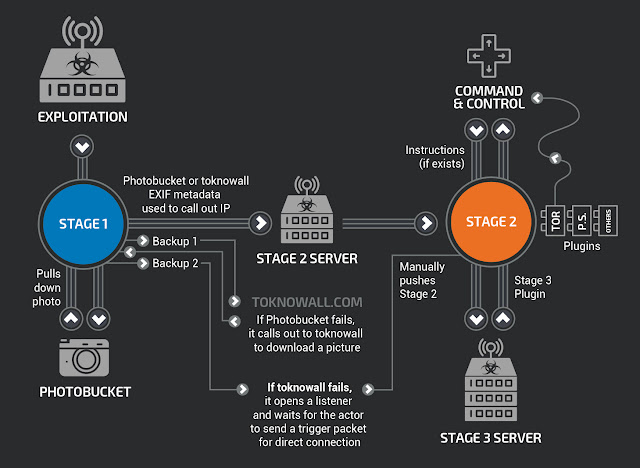
Image by Talos.
Talos Security, a respected IT Security firm, details, how this works. Basically, you connect to a photo server, download some information and addresses hidden in the photo and some instructions and then it downloads a “payload”. The payload starts checking in with a command and control server which in turn decides what it wants to run on your router. This could be anything, a password sniffer, a malware injector, a DDOS agent, it’s really up to the attacker and what they want to do. What is clear though is that they pretty much own ALL the traffic coming in and out of your router and can do what they like.
Since the hack is exposed now the router manufacturers will be working on fixes for this. Also the FBI has taken control of the command and control server and seized the domain which means the servers that were issuing commands are most likely out of commission (for now anyway), once the hack gets shared, expect a bunch of copy cats to use the same exploit. In our opinion, it’s best to get rid of this router for now and find something else. We can make some recommendations if you’re interested.
If this was helpful, let us know. Send us a Tweet, comment on Facebook or peg us on LinkedIn.
The post VPNFilter, Do I Need to Worry appeared first on Proper Sky.



No Comments